 Hello guys, I hope you all are doing great. In today’s tutorial, we will discuss the Difference Between Encryption and Decryption. In a communication system to provide security to the communication over the completer network, two methods are used: encryption and the second one is decryption. The basic difference between them is that in encryption original information or data is transformed into the other coded form or meaningless form. While in decryption is a process through which coded or changed information is transformed into an original form or readable form.
Hello guys, I hope you all are doing great. In today’s tutorial, we will discuss the Difference Between Encryption and Decryption. In a communication system to provide security to the communication over the completer network, two methods are used: encryption and the second one is decryption. The basic difference between them is that in encryption original information or data is transformed into the other coded form or meaningless form. While in decryption is a process through which coded or changed information is transformed into an original form or readable form.
The terms encryption and decryption originated from the cryptology that belongs to the security system of the network. The term cryptology is created with 2 different words cryptography and cryptanalysis. Cryptography is processed through real information transformed into an unreadable form and in cryptanalysis, the transformed information is again converted into the original form of data. In today’s post, we will look at both encryption and decryption and compare them to find their differences. So let’s get started with the Difference Between Encryption and Decryption.
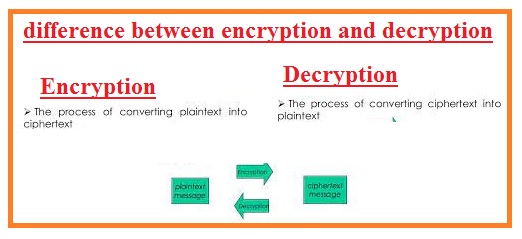
Difference Between Encryption and Decryption
Encryption
- Encryption is a procedure that is used to encode the data transmitted.
- It is used to convert the real data to other forms that are called plaintext.
- It is used to protect data from being lost due to someone.
- It is certain to do encryption through different methods using.
- It is used in military applications for the protection of data transmission.
- It is employed to protect digital information and a different system of information
- It is also employed for civilian purposes.
- IT is used in telecommunication systems to transmit data to users
- Only authorized persons can get to encrypted data
- The process which used to transform original communicated information into a non-real form so any hacker can not get access to the data.
- When data is transferred between two devices it is automatically encrypted with the use of a secret key.
- The encryption process occurs at the information sender side.
- An example of this process is the sending of data between employees and managers in the office.
Decryption
- This process is used to transform coded or transformed information back into the original form.
- During this process, the receiver permits us to transform data from a non-readable form to an original form.
- The process occurs at the receiver side.
- The encrypted data again transferred to its original form is called decryption
- The transformation of information is either automatic or manual.
What is Encryption
- The process through which original information is transferred to other non-readable forms to provide security from lost information.
- It is fact in every transmission of information it is to be taken into consideration that transmitted information should be secure properly. Either wise it is a chance of losing the information.
- Due to this at the sending side, real information is transferred into the coded form.
- This process does not disturb the original signal transmitted but protects from hacking.
- If someone tries to get access to the signal transmitted he will not be able to get access due to transformed information.
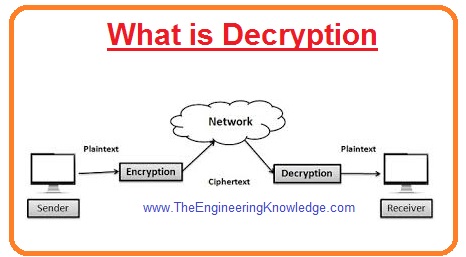
What is Decryption
- The process through which transformed data is again converted into the original information is called decryption.
- The decryption process occurs at a longer distance where data belongs.
- When a signal is transmitted to the receiver after the encryption process receiver gets this information and transformed into its original form.
Comparison between Encryption and Decryption
- The phenomena through which real information is transformed into the coded or ciphertext. But in decryption ciphertext again transforms into an original form or plain text.
- Encryption occurs at the sender’s side while decryption at the receiver’s side.
- The data which is encrypted or after encryption process information called ciphertext. While when data is again converted into the original form called plain text.
- Encryption is an automatic process while decryption is automatic as well manual.
Encryption vs Decryption
Encryption
- In this process, the message is converted in a type of detail that is not easy to read.
- This process is done at the sending point
- its main feature is to transform text in cipher-type of text.
- This process is helpful for the protection of personal data during sent to another person
Decryption
- It is a process that involves converting the useless details of the encryption process into the original message.
- This process occurs at the receiving point
- It used for the conversion of cipher text into real text
- Secret key used for decryption of encrypted data
- Enycroption to decryption pair of keys used.
- The output from decryption is plain text
Read also:
What is the difference between encoding and decryption?
- Encoding is a method that puts a series of characters such as letters, numbers, and symbols in a certain format that is used for transmission.
- Decoding is converting encoded formate again into real form.
What is an example of decryption?
- Decrypting received emails and decrypting encrypted files.
What are the different types of encryption?
- The main types of encryption are symmetric and asymmetric encryption.
What is encryption decryption called?
- Encryption is a process that transforms into secret code that saves real information. The process used for encrypting and decrypting information is called cryptography.
Can encrypted data be decrypted without a key?
- Without the use of a description key encrypted data is not open or unlocked.
What is the weakest encryption type?
- The DES is a symmetric block cipher. It is made for 56-bit keys that are not to be used for modern computing features. It is called weak encryption.
Which encryption is fastest?
- AES is fast and effective for symmetric encryption and RSA and ECC are used for asymmetric encryption.
- Longer encryption used to provide strong security but needed high computational power for working
Read also:
That is a detailed post about the difference between encryption and decryption if you have any queries ask in the comments. Thanks for reading. Have a good day.